TL;DR Google published a paper showing ECDSA can be broken with 500,000 physical qubits, down from 9 million. The online attack phase takes roughly 9 minutes. Bitcoin's block time is 10. The math is real. But the quantum computer isn't what worries me most. Bitcoin needs a post-quantum soft fork that will take 7-15 years of governance trench warfare to ship. Ethereum has funded teams and a concrete roadmap. The gap between those responses tells you more about quantum risk than any qubit count.
Google Quantum AI published a 57-page paper this week titled "Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities", co-authored with Stanford cryptographer Dan Boneh and Ethereum Foundation researcher Justin Drake. The headline: breaking the ECDSA signature scheme securing Bitcoin, Ethereum and most blockchains requires fewer than 500,000 physical qubits. The previous best estimate was 9 million. That's a 20x reduction in three years. They verified their circuit optimizations through the SP1 zkVM, publishing a zero-knowledge proof that the claims are correct without revealing the attack circuits.
The number that matters isn't 500,000. It's 9. The paper introduces a "primed state" optimization splitting Shor's algorithm into two phases: key-independent precomputation the attacker runs in advance, and a key-dependent online phase executing once a public key is revealed. That online phase takes roughly 9 minutes. Bitcoin's block confirmation time is 10. When you broadcast a Bitcoin transaction, your public key appears in the mempool. A quantum attacker with sufficient hardware could derive your private key, construct a competing transaction, steal your funds before your original confirms. The attack surface isn't just dormant wallets. It's live transactions.
I've been in crypto since 2012. I run infrastructure at a major cryptocurrency exchange. The dismissals are wrong. So is the panic. The real threat isn't the quantum computer. It's the governance paralysis that will prevent the largest blockchain from responding in time.
ECDSA is a softer target than RSA
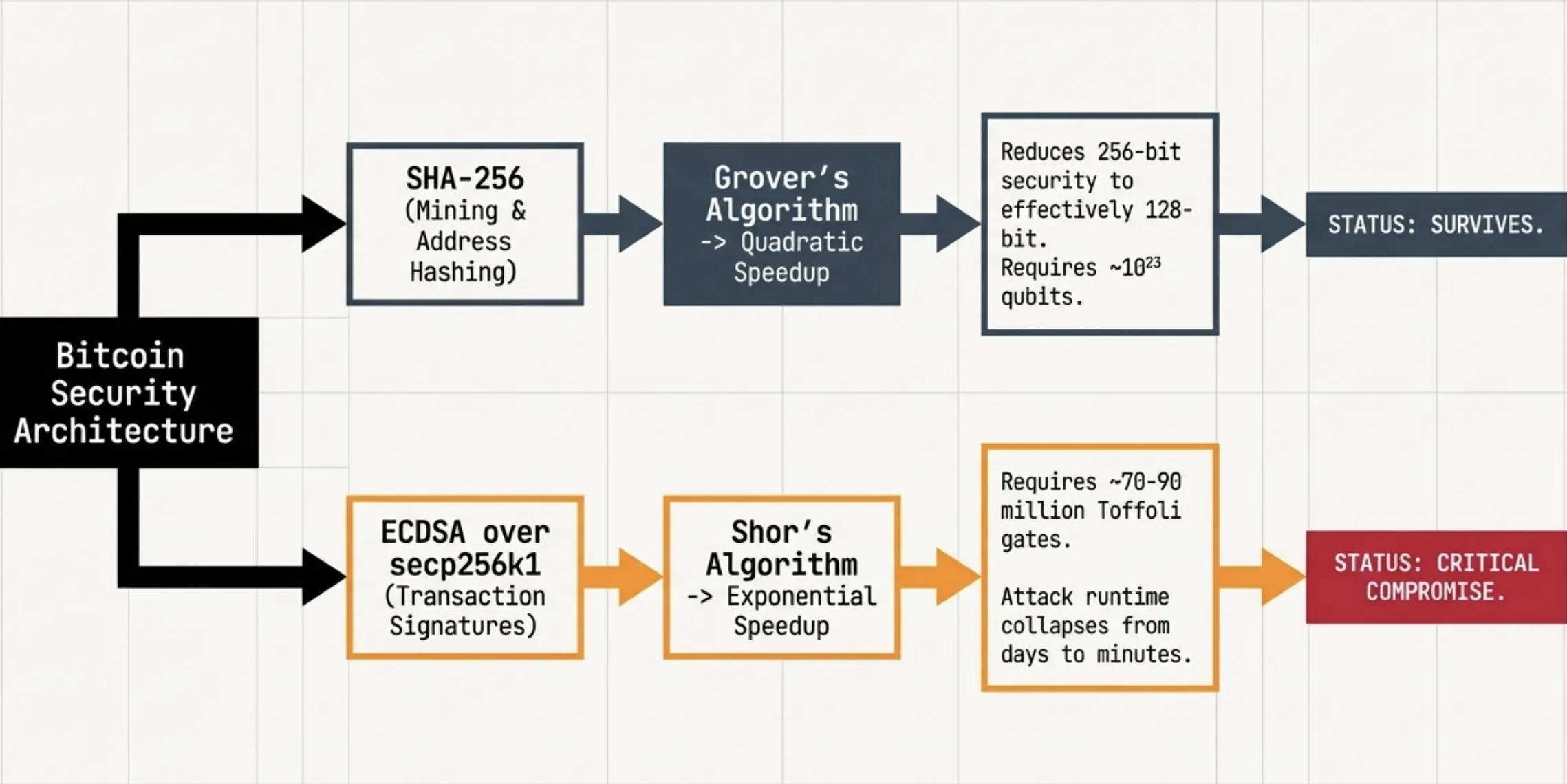
Bitcoin's security rests on two cryptographic foundations: SHA-256 for mining and address hashing, ECDSA over secp256k1 for transaction signing. Quantum computers threaten these differently.
SHA-256 is fine. Grover's algorithm provides a quadratic speedup against hash functions, reducing 256-bit security to effectively 128 bits. Still astronomically hard. Quantum mining at Bitcoin's current difficulty would require on the order of 10²³ qubits. SHA-256 will survive quantum computing.
ECDSA is the problem. Shor's algorithm provides an exponential speedup against the Elliptic Curve Discrete Logarithm Problem. Breaking 256-bit ECC requires roughly 70-90 million Toffoli gates. Breaking RSA-2048 requires about 6.5 billion. A ~100x difference. Attack runtime collapses to minutes for ECC, stays at days for RSA.
The practical consequence is one the crypto industry doesn't want to hear. The TLS connections protecting your bank's website (mostly RSA-based) will remain quantum-secure longer than Bitcoin's transaction signatures. The asset class marketing itself as the most secure form of money is, against this specific threat, more vulnerable than the legacy financial system it claims to replace.
Banks have three structural advantages. Centralized decision-making: when NIST says "deprecate ECC by 2030", they comply. No consensus debate. JPMorgan has already deployed a quantum-safe communication network. Symmetric encryption as a fallback: AES-256 for data at rest remains quantum-resistant, and their vulnerability is the key exchange layer in TLS, upgradeable without touching data protection. Crypto has no quantum-safe layer underneath. Retroactive data protection: banks can re-encrypt historical data and rotate keys. Blockchain histories are permanent and public. Every exposed public key is already harvestable. The "harvest now, decrypt later" risk is existential for blockchains in a way it simply isn't for traditional finance.
6.9 million BTC with exposed keys
The paper identifies roughly 6.9 million BTC (32% of circulating supply, north of $450 billion) across varying degrees of quantum vulnerability. P2PK addresses from Bitcoin's earliest era store the full public key on-chain with no hash protection: 1.7 million BTC, including Satoshi's estimated 1.1 million across ~22,000 early coinbase outputs. Reused P2PKH addresses expose another ~4.9 million BTC.
The twist is Taproot. Bitcoin's most recent major upgrade (activated 2021) stores tweaked public keys directly in locking scripts, visible on-chain without hash protection. Only ~0.1% of supply uses Taproot today. But it's the foundation for Lightning Network, BitVM and virtually every scaling solution Bitcoin is building toward. Google called this a "quantum security regression". The community spent years debating and celebrating Taproot for its privacy and smart contract capabilities. Nobody adequately modeled the quantum attack surface it introduced.
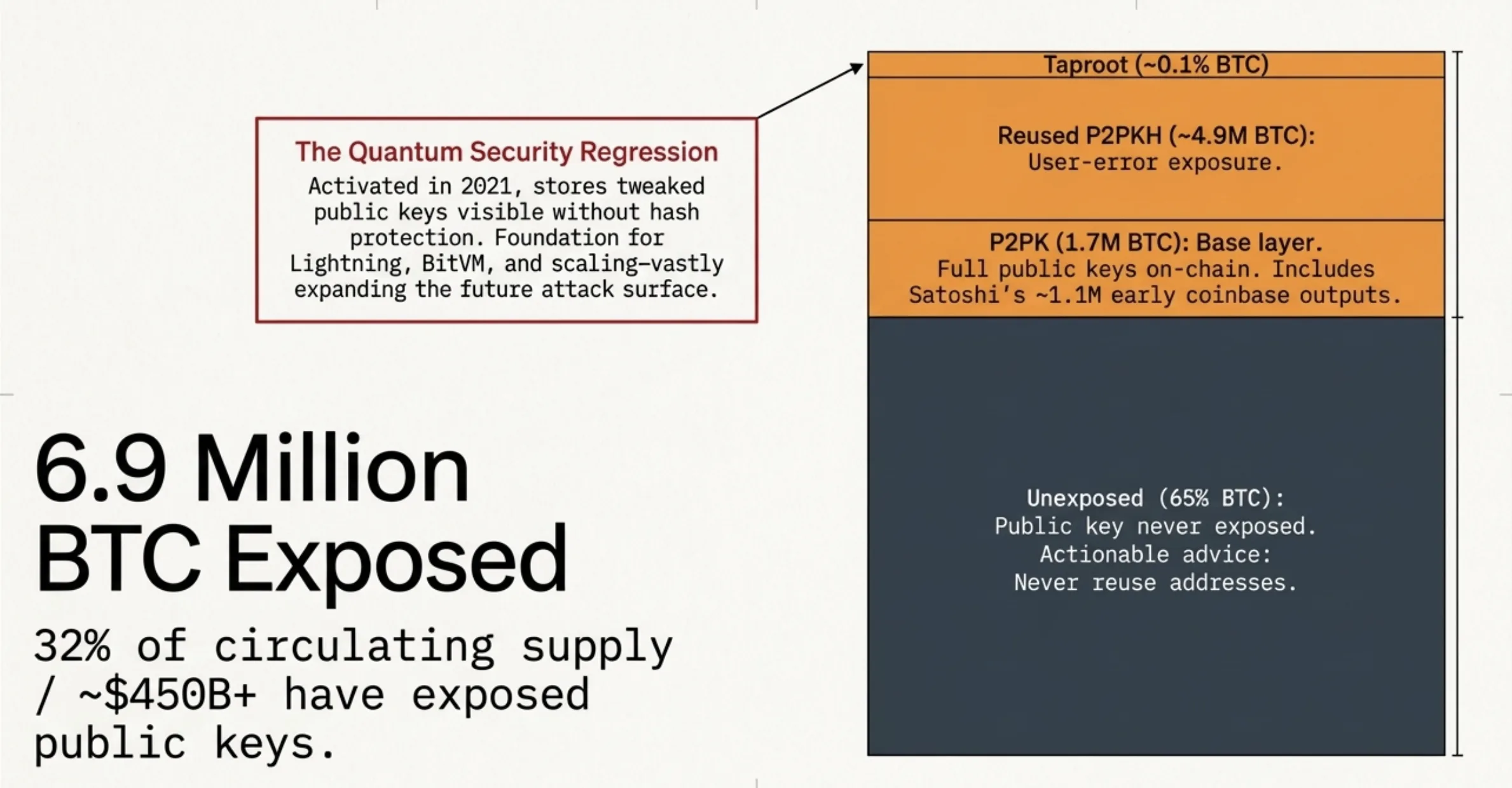
Roughly 65% of Bitcoin's supply remains in addresses where the public key has never been exposed. Never reuse addresses. Avoid Taproot for long-term storage until post-quantum migration is clearer. That costs nothing and meaningfully reduces your exposure.
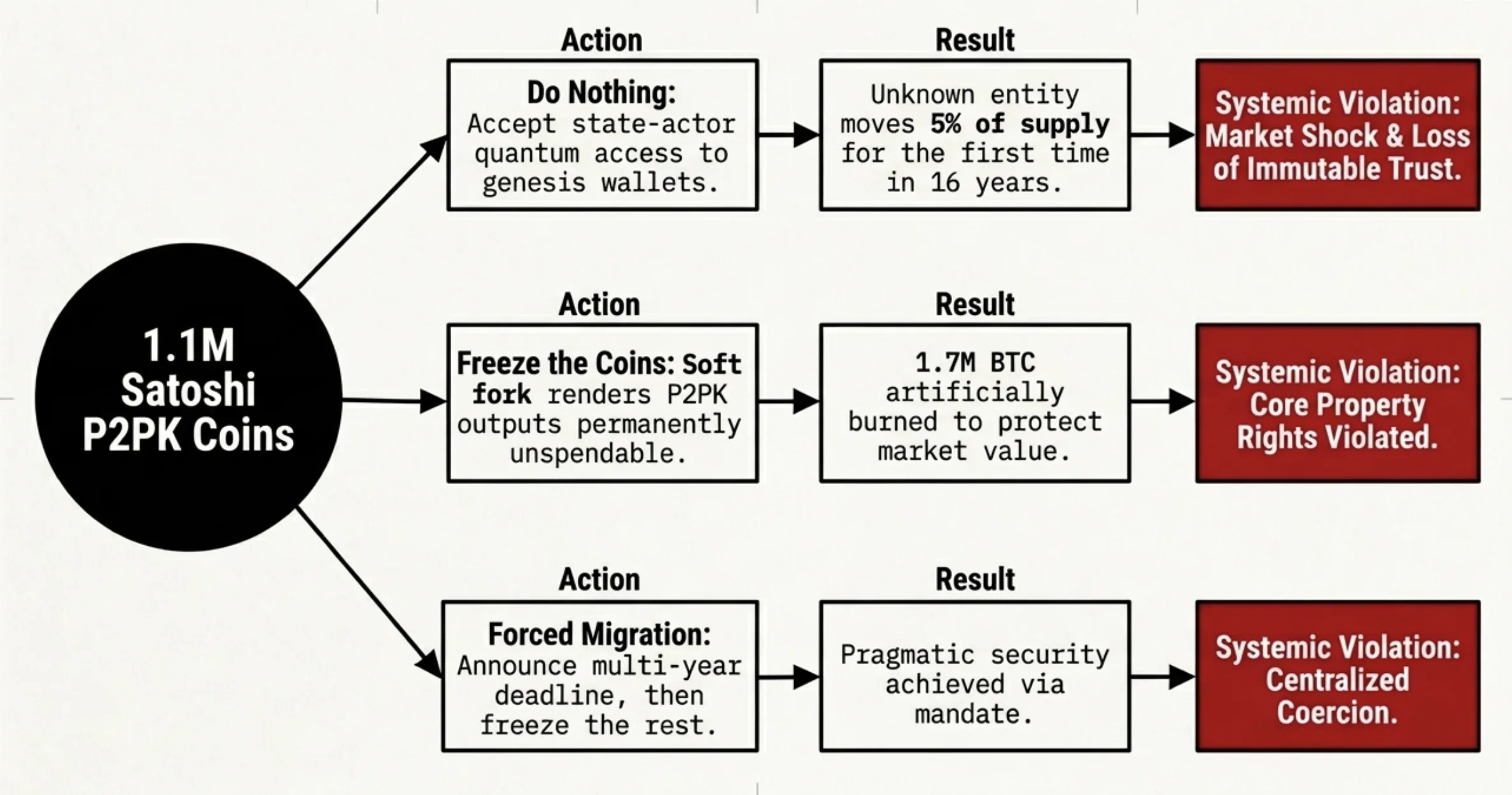
Three options for Satoshi's coins, all bad
Satoshi's ~1.1 million BTC in P2PK cannot be migrated. After 16 years of silence, the most likely scenario is that these coins will become quantum-accessible to whoever builds a cryptographically relevant quantum computer first. Probably a state actor.
Do nothing: accept that a quantum attacker moves 5% of all Bitcoin for the first time in 16 years, controlled by an unknown entity. Preserves immutability. Creates a potential market shock. Freeze the coins: a soft fork renders P2PK outputs unspendable, burning 1.7 million BTC. Protects the market. Violates the most fundamental property right Bitcoin was built to guarantee. Forced migration with a deadline: announce a multi-year window for vulnerable outputs to migrate, freeze what remains. Pragmatic. Requires centralized coordination that Bitcoin's governance model was designed to prevent.
Every option violates a core principle. I don't think the community will reach consensus on any of them. That governance paralysis is the real risk, not the quantum computer itself.
Bitcoin can't ship fast enough
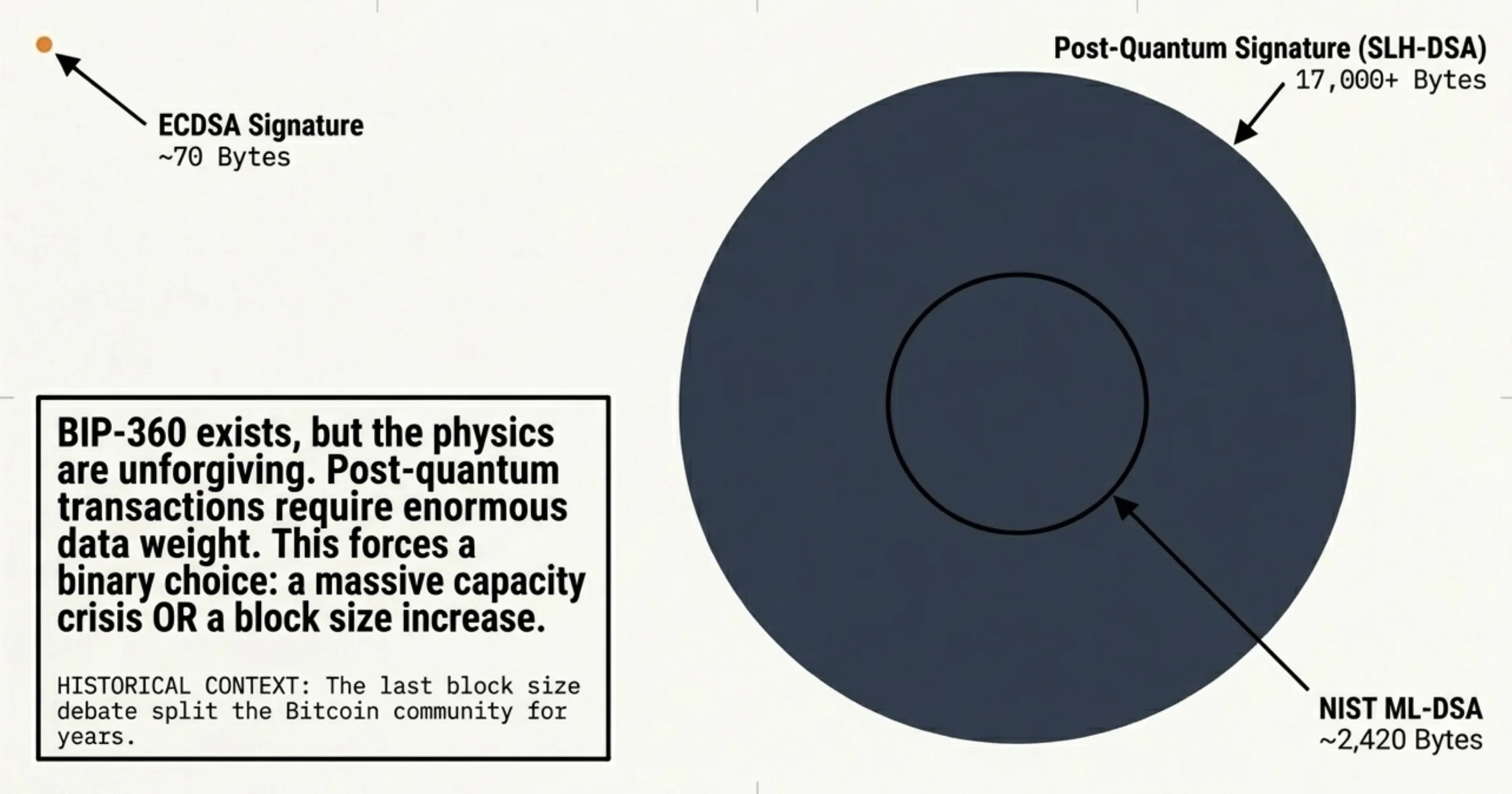
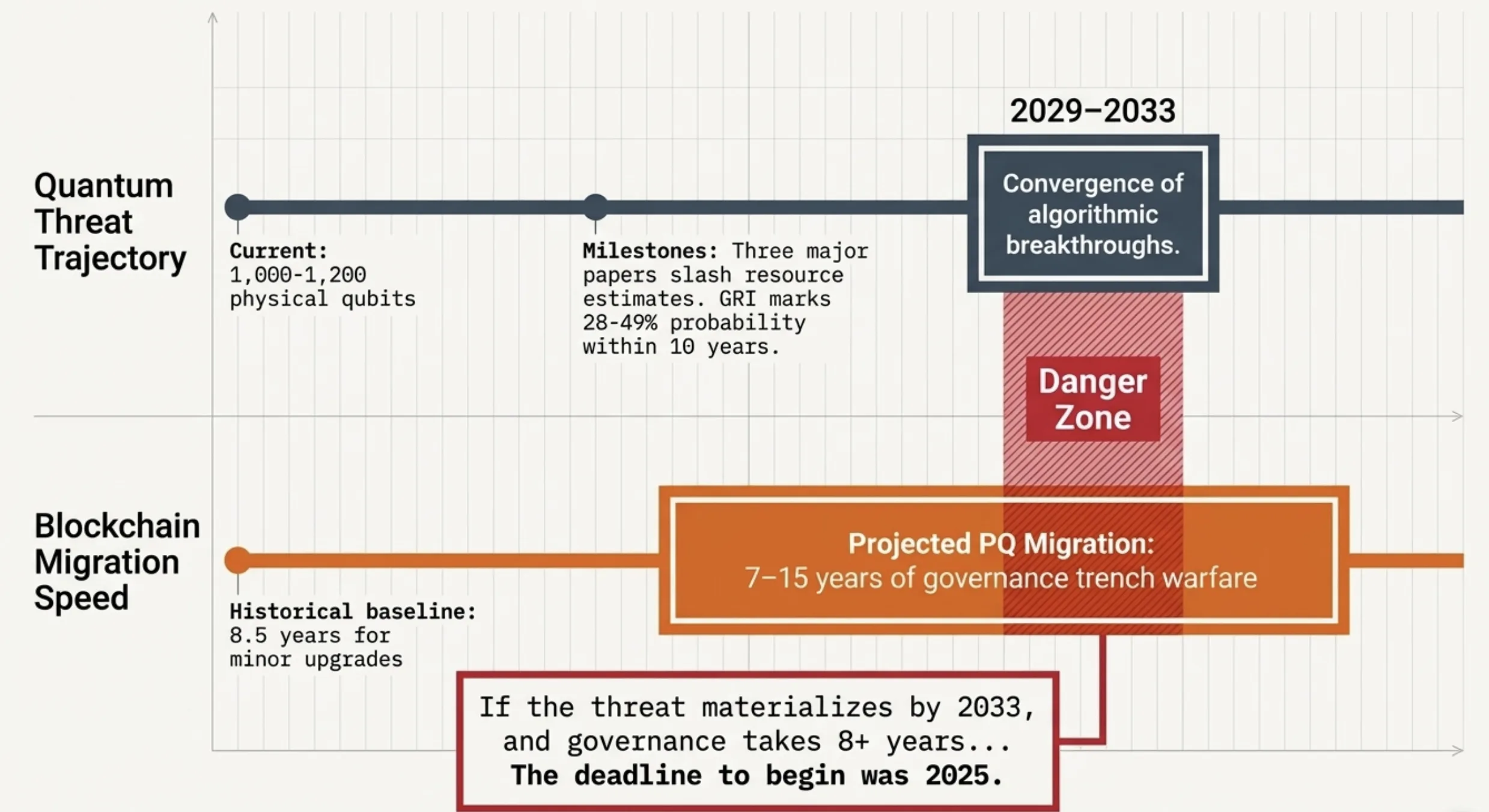
BIP-360 is the most mature technical proposal for quantum-resistant Bitcoin signatures. BTQ Technologies deployed it on a testnet in March. The design is thoughtful. But SegWit took roughly 8.5 years from concept to broad adoption. Taproot took about 7.5. Post-quantum migration is more contentious than either.
Post-quantum signatures are enormous. NIST's ML-DSA produces signatures around 2,420 bytes. SLH-DSA can exceed 17,000. Compare that to ECDSA's 70. Bitcoin's block weight limit means post-quantum transactions would dramatically reduce throughput, forcing either a capacity crisis or a block size increase. The last block size debate split the community for years.
Nic Carter called Bitcoin's quantum response "worst in class". Peter Todd has dismissed the threat timeline as "laughable". Adam Back maintains CRQCs are 20-40 years away. Chaincode Labs characterized every Bitcoin PQ initiative as "early and exploratory" in May 2025. That assessment still holds. The realistic migration timeline is 7-15 years from the moment political will crystallizes.
Ethereum has a leader. That matters now.
Ethereum shares Bitcoin's ECDSA vulnerability. Over 65% of all Ether has exposed public keys because Ethereum's account model reveals keys on the first outgoing transaction and encourages reuse. In raw exposure terms, Ethereum is worse.
But Vitalik Buterin published a quantum emergency hard fork plan in March 2024. By February 2026 he'd outlined fixes for all four quantum-vulnerable protocol components. EIP-8141 introduces native account abstraction decoupling transaction authorization from ECDSA entirely. The Ethereum Foundation formed a dedicated Post-Quantum Security team in January 2026, launched pq.ethereum.org, offered $2 million in research prizes, published a roadmap with seven hard forks through 2029 targeting post-quantum L1.
Justin Drake co-authored the Google paper. When an Ethereum Foundation researcher helps quantify the threat and the Foundation responds with funded teams within months, that's a fundamentally different organizational response than what Bitcoin Core has produced.
Centralized research coordination is a philosophical weakness for Ethereum. In this specific scenario, it's an overwhelming strategic advantage.
The timeline is uncertain. The trajectory is not.
Today's largest quantum computers have roughly 1,000-1,200 physical qubits. We need ~500,000 to break ECDSA. Nobody is cracking Bitcoin tomorrow.
Three papers in three months (Gidney on RSA, Chevignard et al. on ECDLP, this Google paper) slashed resource estimates faster than hardware is scaling. Multiple independent projections converge on 2029-2033 for cryptographically relevant capability against elliptic curves. The Global Risk Institute's 2025 survey found 28-49% probability within 10 years.
Hardware progress is relatively predictable. Algorithmic breakthroughs are discontinuous. Every time someone proves a new qubit floor, the floor breaks within two years. I'd put the probability of a state-level actor possessing ECDSA-breaking capability by 2033 at roughly 15-25%. If the threat materializes by 2033 and the governance process takes 8 years, the deadline for starting was 2025.
Where this argument breaks
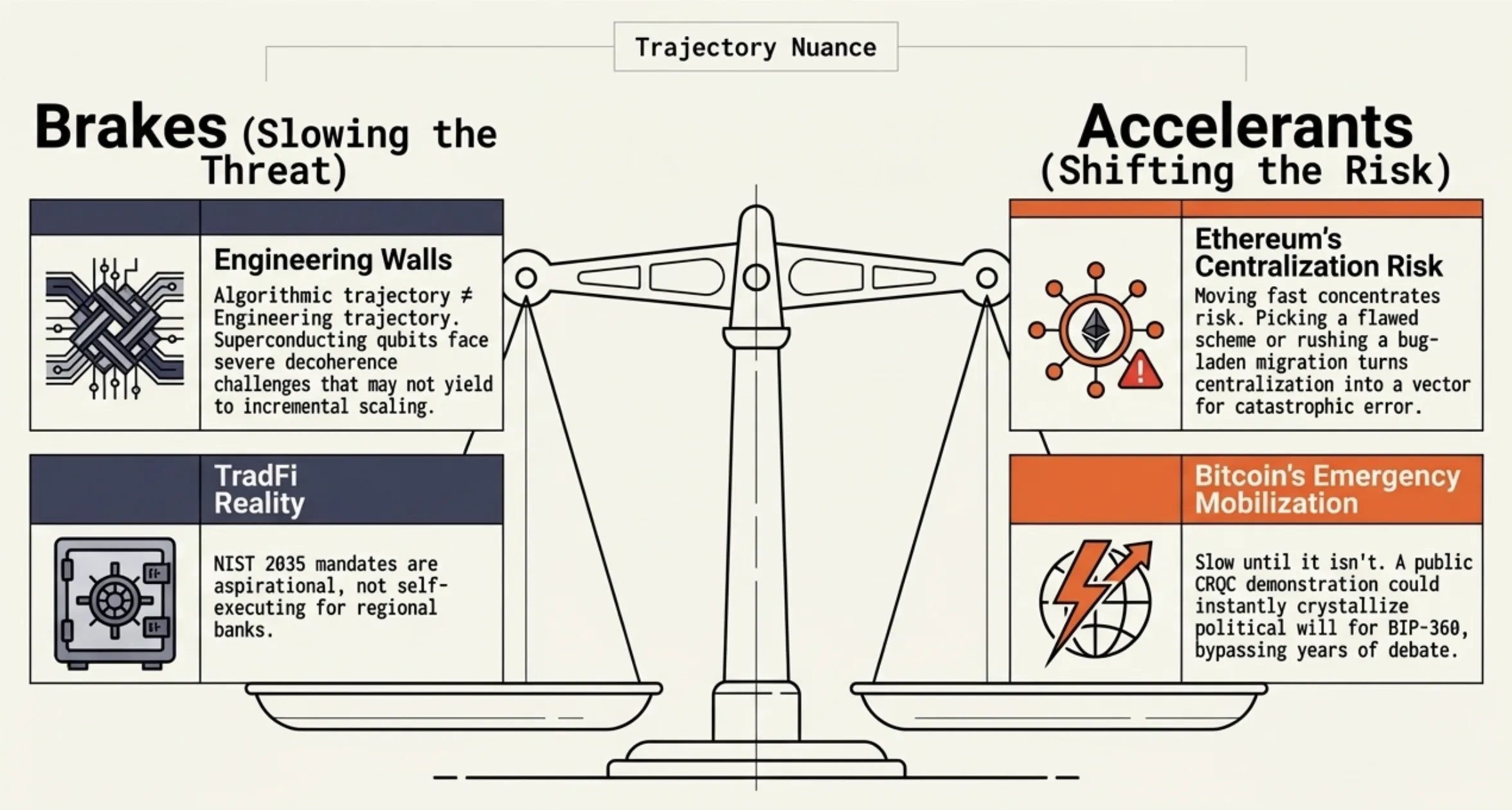
I might be overweighting the governance risk. Bitcoin has mobilized before when existential threats became concrete. The community activated SegWit after years of deadlock once urgency was undeniable. If a credible CRQC demonstration against a smaller elliptic curve happens publicly, political will for BIP-360 could crystallize fast. Bitcoin's governance is slow until it isn't.
I might be too confident in the timeline convergence. Three papers finding similar qubit counts could reflect shared assumptions rather than independent verification. If Gidney, Kim and Chevignard all build on the same foundational techniques, an error in that foundation propagates through all estimates. The gap between "feasible in theory" and "engineerable in practice" has historically been larger in quantum computing than any other paradigm. Superconducting qubits face decoherence challenges that may not yield to incremental scaling. The 500,000 qubit figure assumes engineering problems are solved that haven't been solved yet. I'm treating the algorithmic trajectory as a proxy for the engineering trajectory. Those could diverge sharply.
The Ethereum advantage may be temporary. Coordinated leadership enables speed in crisis response. It also concentrates the risk of being wrong. If the Foundation's post-quantum choices are flawed (selecting a scheme that's later broken, introducing bugs in a rush migration), the centralization that enabled speed becomes the vector for catastrophic error. Bitcoin's slow consensus is also a filter against premature commitments.
My comparison to traditional finance oversells the advantage. NIST can mandate ECC deprecation by 2035. That doesn't mean every regional bank complies on schedule. The date is aspirational, not self-executing.
The most honest statement: the probability distribution over quantum timelines is wide enough that both dismissers and alarmists can cite the same data. The question is whether the cost of acting early (years of migration for a threat that doesn't materialize on schedule) is lower than the cost of acting late (no quantum-resistant signatures when a CRQC arrives). That asymmetry drives everything here. But asymmetric reasoning has a known failure mode: it justifies any precaution if you frame the downside dramatically enough. I'm aware I might be doing exactly that.
The clock and the committee
Google's paper didn't change the physics. It changed the math. The trajectory was already here. Now it has coordinates.
The protocols that treat post-quantum migration as a priority starting this year will have time. The ones waiting for consensus, or dismissing the timeline, or delaying because governance is hard, will discover that decentralized decision-making is a feature in calm seas and a liability when the clock is running. The cryptographic foundation has an expiration date we can now estimate. Whether the industry can govern itself fast enough to respond is a harder problem than any quantum circuit.